EV cybersecurity risks in 2025 are, like, totally a big deal. We’re talking about everything from sneaky software vulnerabilities that could let hackers take control of your ride to data breaches exposing your personal info. Think about it: your car is basically a super-connected computer on wheels, and that makes it a prime target for cyberattacks. This isn’t just about annoying glitches; we’re talking about potential safety hazards and serious privacy violations.
Let’s dive into the nitty-gritty and see what the future holds.
The increasing reliance on software, the explosion of connected car features (like V2X communication), and the growing sophistication of cybercriminals all contribute to a heightened risk profile for electric vehicles. We’ll examine vulnerabilities in software, data security protocols, and physical security measures, as well as the role of AI in both enhancing and potentially compromising EV security. We’ll also explore the implications for consumers, manufacturers, and policymakers.
Software Vulnerabilities in EV Systems: EV Cybersecurity Risks In 2025
EVs are increasingly complex systems, integrating sophisticated software into nearly every aspect of their operation. This reliance on software introduces significant cybersecurity risks, particularly as the software controlling critical functions like powertrains, battery management, and charging infrastructure becomes more intricate. These vulnerabilities represent a serious threat, potentially leading to vehicle malfunctions, data breaches, and even physical harm.The potential for software vulnerabilities in EVs is substantial.
The powertrain control unit (PCU), for example, manages the flow of power from the battery to the motor, and vulnerabilities here could allow an attacker to manipulate acceleration, braking, or steering. Similarly, the battery management system (BMS) controls charging, discharging, and overall battery health. Compromising the BMS could lead to overcharging (causing fires), rapid discharging (leaving the driver stranded), or even complete battery failure.
The charging infrastructure itself, including charging stations and related software, is also vulnerable. Malicious actors could potentially interfere with charging processes, causing damage to the vehicle’s battery or even stealing sensitive data.
Outdated Software and Infrequent Updates
Outdated software and infrequent updates significantly amplify the cybersecurity risks associated with EVs. Many legacy systems lack robust security features, making them susceptible to known exploits. Furthermore, manufacturers often lag in releasing security patches, leaving vehicles vulnerable for extended periods. This is particularly concerning given the constant evolution of hacking techniques. Consider the situation with some older model infotainment systems; their susceptibility to remote hacking, through readily available exploits, highlights the dangers of neglecting software updates.
A delayed response to known vulnerabilities in an EV’s software could have far more severe consequences than a compromised infotainment system. For instance, a delayed patch for a vulnerability in the BMS could lead to a battery fire.
Examples of Software Vulnerabilities in Connected Car Systems
Several vulnerabilities exploited in connected car systems highlight the potential risks facing EVs. For instance, attacks targeting the infotainment system have allowed hackers to gain access to personal data, control vehicle functions, or even remotely disable the car. While seemingly less critical than compromising a powertrain system, these attacks demonstrate the broader principle of interconnectedness and the potential for escalation.
A successful attack on a less critical system might provide a foothold to access more sensitive components, like the BMS or PCU. Another example comes from attacks that exploit vulnerabilities in the vehicle’s telematics system, which collects and transmits data about vehicle performance and location. Compromising this system could expose sensitive driver information or allow for vehicle tracking.
These vulnerabilities are directly transferable to EVs, given the increasing integration of connected car features.
Hypothetical Attack Scenario: Compromising an EV’s Software
Imagine a scenario where a malicious actor discovers a vulnerability in the over-the-air (OTA) update mechanism of an EV’s BMS. By exploiting this vulnerability, they could inject malicious code into a seemingly legitimate software update. This malicious code could subtly alter the BMS’s charging algorithms, causing it to slowly overcharge the battery over time. This slow, insidious attack might go undetected for weeks or months, eventually leading to a battery fire or catastrophic failure.
The attack could be further amplified if the attacker also compromised the vehicle’s telematics system, allowing them to monitor the battery’s condition remotely and adjust the attack accordingly. This illustrates how seemingly minor vulnerabilities can be exploited to cause significant damage.
EV cybersecurity is gonna be a huge deal in 2025, with hackers potentially targeting everything from braking systems to navigation. So, the news on the Lightyear Solar EV availability in the US is interesting, because a new, cutting-edge car like that could become a prime target for exploits. We need to be thinking about these security risks way before these vehicles hit the road.
Data Breaches and Privacy Concerns
Electric vehicles (EVs) are becoming increasingly sophisticated, incorporating advanced technologies like internet connectivity, GPS tracking, and over-the-air updates. This interconnectedness, while offering convenience and enhanced features, significantly expands the attack surface and introduces substantial data breach and privacy risks. The sheer volume of sensitive data collected by EVs necessitates a robust security framework to protect user information and maintain trust.EVs collect a wide range of data, much of it highly sensitive.
This includes personal information like driver identification, location data (often precise GPS coordinates), driving habits (speed, acceleration, braking patterns), vehicle diagnostics, charging history, and even in-car camera footage. A breach could expose this information to malicious actors, leading to identity theft, stalking, insurance fraud, targeted advertising, or even blackmail. The risk is compounded by the fact that much of this data is transmitted wirelessly, creating vulnerabilities to interception and manipulation.
Methods for Securing Data Transmission
Secure data transmission between EVs, charging stations, and cloud services requires a multi-layered approach. This includes employing strong encryption protocols (like TLS 1.3 or higher) for all communication channels. Data should be encrypted both in transit and at rest, using robust algorithms resistant to known attacks. Regular security audits and penetration testing are crucial to identify and address vulnerabilities before they can be exploited.
Implementing robust authentication mechanisms, such as multi-factor authentication, adds another layer of security, making it harder for unauthorized individuals to access the data. Furthermore, the use of secure hardware components, like tamper-resistant chips, can further protect sensitive information from unauthorized access or manipulation. Finally, adhering to industry best practices and relevant data protection standards, such as those defined by ISO 27001, is essential for maintaining a high level of data security.
Legal and Ethical Implications of Data Breaches
Data breaches involving EV user information carry significant legal and ethical implications. Companies face potential lawsuits for negligence, violation of privacy laws (like GDPR or CCPA), and reputational damage. Users could suffer financial losses, emotional distress, and identity theft. Ethically, companies have a responsibility to protect user data and be transparent about their data handling practices. A breach undermines trust and can have far-reaching consequences for the entire EV ecosystem.
Regulations around data privacy are evolving rapidly, and companies must stay abreast of these changes to avoid legal repercussions and maintain ethical standards. Proactive measures, including robust incident response plans, are critical for minimizing the impact of a breach and demonstrating a commitment to data protection.
Comparison of Data Security Measures
| Manufacturer | Data Encryption Method | Data Storage Location | Incident Response Plan |
|---|---|---|---|
| Tesla | AES-256, TLS 1.3+ | Tesla servers, potentially on-device | Publicly available information on handling security incidents, though specifics are limited. |
| General Motors | Proprietary encryption methods, likely incorporating industry standards | GM servers, potentially on-device | Details are not publicly available, but likely adheres to industry best practices. |
| Ford | AES-256, TLS 1.3+ (likely) | Ford servers, potentially on-device | Limited public information; likely incorporates standard security protocols. |
| Volkswagen | Likely incorporates industry-standard encryption methods | Volkswagen servers, potentially on-device | Information not readily available publicly. |
Vehicle-to-Everything (V2X) Communication Risks
V2X communication, a cornerstone of autonomous driving and smart cities, allows vehicles to exchange information with other vehicles, infrastructure, and pedestrians. While promising enhanced safety and efficiency, this interconnectedness introduces significant cybersecurity vulnerabilities that need careful consideration, especially in the context of EVs which are increasingly reliant on software and network connectivity. Failing to address these risks could lead to serious consequences, ranging from minor inconveniences to catastrophic accidents.V2X systems utilize various communication technologies, each with its own security strengths and weaknesses.
Understanding these differences is crucial for developing effective security measures.
Security Protocols in V2X Communication Systems
Different V2X communication systems employ diverse security protocols. Dedicated Short-Range Communications (DSRC), using 802.11p, often relies on cryptographic techniques like message authentication codes (MACs) and digital signatures to ensure message integrity and authenticity. Cellular V2X (C-V2X), leveraging cellular networks (4G/5G), benefits from the existing security infrastructure of cellular networks, including authentication and encryption mechanisms. However, the security of both systems depends heavily on the implementation and proper configuration of these protocols.
A weakness in any part of the system, such as a poorly implemented cryptographic algorithm or a vulnerable authentication mechanism, can compromise the entire communication channel. For instance, a flaw in the key management system could allow an attacker to eavesdrop on or manipulate communications.
Examples of V2X Attacks and Their Consequences
Several potential attacks targeting V2X communication exist. A common concern is spoofing, where an attacker sends false information, potentially causing a vehicle to misinterpret its surroundings. For example, an attacker could spoof a stop sign message, leading to a collision. Another significant risk is denial-of-service (DoS) attacks, which flood the network with traffic, preventing legitimate communications from reaching their destination.
This could disable critical safety features or disrupt traffic flow, causing widespread congestion. Furthermore, an attacker could exploit vulnerabilities in the security protocols to eavesdrop on private information exchanged between vehicles, such as location data or driver identification, leading to privacy violations. The consequences of these attacks can range from minor disruptions to severe accidents and significant privacy breaches.
A successful attack could potentially compromise the safety and security of not only individual vehicles but also the entire transportation system.
Best Practices for Securing V2X Communication in Autonomous Driving Systems
Robust security measures are paramount for the safe deployment of V2X in autonomous driving. This includes employing strong cryptographic algorithms, secure key management practices, and regular security updates. Implementing robust authentication mechanisms to verify the identity of communicating entities is crucial. Furthermore, intrusion detection and prevention systems are essential for monitoring network traffic and identifying malicious activities.
Regular penetration testing and vulnerability assessments can help identify and mitigate potential weaknesses. Finally, collaboration and standardization across different V2X systems are vital to ensure interoperability and consistent security levels. A layered security approach, incorporating multiple security mechanisms, is highly recommended to mitigate the risks associated with V2X communication. This layered approach should consider the vulnerabilities at each level of the communication stack, from the physical layer to the application layer.
For example, secure boot processes and runtime monitoring are vital for preventing attacks that target the vehicle’s onboard systems.
Over-the-Air (OTA) Update Vulnerabilities
Over-the-air (OTA) updates are crucial for keeping EV software current, adding features, and patching security flaws. However, this convenient mechanism introduces significant security risks if not properly implemented and secured. The inherent complexity of the process, coupled with the increasing sophistication of cyberattacks, makes OTA updates a prime target for malicious actors.OTA updates rely on a complex chain of communication and verification steps, each representing a potential point of failure.
Attackers can exploit vulnerabilities at various stages, from compromising the update server to injecting malicious code into the update package itself. This can lead to serious consequences, ranging from minor malfunctions to complete vehicle control compromise.
OTA Update Server Compromise
Compromising the update server is a significant threat. If attackers gain control of the server, they can distribute malicious updates to all connected vehicles. This could involve replacing legitimate updates with malware designed to steal data, disable safety features, or even take control of the vehicle’s systems. Robust security measures, such as multi-factor authentication, intrusion detection systems, and regular security audits, are crucial to mitigate this risk.
A well-designed server architecture that incorporates redundancy and fail-safes is also paramount. For example, a geographically distributed server infrastructure could reduce the impact of a single point of failure or attack.
Malicious Code Injection into Update Packages
Attackers might attempt to inject malicious code directly into the update package itself. This could involve tampering with the update package during its creation, transmission, or installation. Methods for achieving this might include exploiting vulnerabilities in the software development lifecycle, compromising the update signing process, or intercepting the update package during transmission. This could lead to the execution of arbitrary code on the vehicle’s systems, giving attackers complete control.
A strong focus on secure coding practices, robust digital signatures, and secure communication protocols are essential for preventing this type of attack. Imagine a scenario where an attacker replaces a legitimate firmware update with a modified version that allows remote unlocking of the vehicle.
Verification of Update Integrity and Authenticity
Verifying the integrity and authenticity of OTA updates is critical. This involves ensuring that the update hasn’t been tampered with and that it originated from a trusted source. Digital signatures, cryptographic hash functions, and certificate-based authentication are commonly used techniques. These methods allow the vehicle to verify that the update package hasn’t been modified and that it came from a legitimate source.
For example, a digital signature would verify that the update was signed by the manufacturer’s private key, proving its authenticity. The vehicle then uses the manufacturer’s public key to verify the signature. A mismatch would indicate a compromised update.
Securing the OTA Update Mechanism
Securing the OTA update mechanism involves a multi-layered approach. This includes using secure communication protocols (like HTTPS) to protect the transmission of update packages, implementing robust authentication and authorization mechanisms to verify the identity of the vehicle and the update server, and employing secure boot processes to ensure that only authorized code is executed during the update process. Regular security audits and penetration testing are also vital to identify and address vulnerabilities before they can be exploited.
Furthermore, implementing a rollback mechanism to revert to a previous software version in case of a failed or malicious update is a crucial safety feature. A comprehensive security architecture encompassing all these elements will significantly reduce the risk of successful attacks.
Okay, so EV cybersecurity in 2025 is gonna be a huge deal, right? Think about all the potential attack vectors – we’re talking everything from remote hacks to physical tampering at charging stations. And speaking of charging stations, check out this article about the planned expansion of EV charging stations along Route 66 in 2025 ; it highlights just how many more vulnerable points we’ll have to secure.
That’s why robust cybersecurity measures for these stations are absolutely critical to prevent widespread network disruptions and data breaches.
Physical Security Threats to EVs
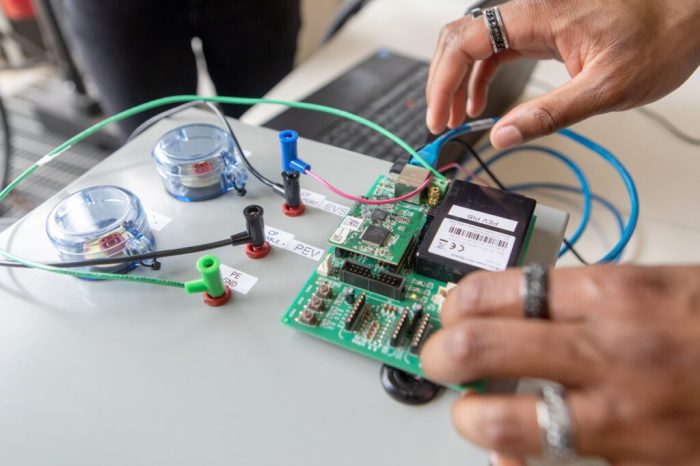
Electric vehicles, while offering significant environmental benefits, present unique physical security challenges. Unlike traditional gasoline-powered cars, EVs contain high-value components like expensive battery packs and sophisticated electronics that are attractive targets for theft and vandalism. Furthermore, the reliance on charging infrastructure introduces new vulnerabilities, making physical security a critical concern for both vehicle owners and manufacturers.EV battery packs are particularly vulnerable.
These batteries, often containing valuable materials like lithium-ion, are expensive to replace and can be easily targeted for theft or malicious damage. The charging port, a necessary component for recharging the vehicle, is also a potential entry point for attacks. Physical access to the charging port could enable malicious actors to install malicious devices, potentially disrupting the charging process or even gaining unauthorized access to the vehicle’s systems.
Beyond theft and malicious damage, environmental factors like extreme temperatures or physical impacts could also damage the battery pack or other sensitive components, highlighting the need for robust physical protection.
Battery Pack Protection Mechanisms
Protecting EV battery packs requires a multi-layered approach. This includes robust physical casing designed to withstand impacts and tampering, integrated monitoring systems to detect unusual activity or environmental conditions (like excessive heat), and potentially, GPS tracking to aid in recovery in case of theft. Manufacturers are increasingly incorporating tamper-evident seals and advanced locking mechanisms to deter unauthorized access.
Furthermore, the use of secure enclosures and strategically placed sensors can enhance detection capabilities, alerting owners or authorities to potential threats. Consider a system where sensors detect unauthorized access attempts or unusual vibrations, triggering an alert to the owner and potentially immobilizing the vehicle.
Charging Port Security Measures
The charging port presents a unique challenge, as it requires accessibility for legitimate charging. However, this accessibility can be exploited by malicious actors. One solution is the use of biometric authentication systems, similar to those found on smartphones or laptops, requiring a fingerprint or facial scan before charging can commence. Another approach involves sophisticated locking mechanisms that only unlock when the vehicle recognizes the charging station through secure communication protocols.
Furthermore, incorporating tamper detection sensors within the charging port itself can help detect attempts to bypass security measures or install malicious devices. Think of it as a combination of physical locks and sophisticated electronic verification.
Physical Security Measures from Other Industries
Many physical security measures used in other industries are directly applicable to EVs. For example, the use of tamper-evident seals, widely employed in pharmaceutical and high-value goods industries, can help detect unauthorized access to the battery pack or other sensitive components. Similarly, GPS tracking systems, commonly used in logistics and fleet management, can be integrated into EVs to track their location and aid in recovery in case of theft.
Finally, advanced surveillance systems, including cameras and motion detectors, could be incorporated into charging stations to monitor activity and deter theft or vandalism. These measures, adapted and refined for the specific context of EVs, can significantly enhance physical security.
A System for Detecting and Responding to Physical Attacks
A comprehensive system for detecting and responding to physical attacks on an EV would integrate several key components. This includes a network of sensors throughout the vehicle monitoring for impacts, vibrations, unauthorized access attempts, and environmental anomalies. This sensor data would be processed by an onboard computer that uses machine learning algorithms to distinguish between normal and suspicious activity.
Upon detecting a potential attack, the system could trigger several responses, such as immobilizing the vehicle, alerting the owner via a mobile app, and notifying authorities. The system could also record data on the attack, providing valuable evidence for investigation and future security improvements. This approach would provide a real-time, proactive defense against a range of physical threats.
The Role of Artificial Intelligence (AI) in EV Cybersecurity

AI is rapidly transforming various sectors, and its impact on EV cybersecurity is significant. It offers the potential to enhance security dramatically, but also introduces new vulnerabilities that need careful consideration. This section explores the dual nature of AI’s role in protecting and potentially compromising electric vehicle security.AI can significantly bolster EV cybersecurity through its ability to analyze massive datasets, identify patterns indicative of malicious activity, and respond to threats in real-time.
This surpasses the capabilities of traditional rule-based systems, which often struggle to keep up with the ever-evolving tactics of cybercriminals. The speed and accuracy of AI-driven threat detection and response are key advantages.
AI-Enhanced Cybersecurity Measures in EVs
AI algorithms can be trained on vast amounts of data representing normal vehicle behavior and known attack patterns. This allows them to establish a baseline of “normal” operation and readily detect deviations suggesting a cyberattack. For example, an AI system might monitor sensor data, network traffic, and control system activity, flagging unusual spikes, inconsistencies, or unauthorized access attempts.
Furthermore, AI can automate responses to detected threats, such as isolating compromised systems, initiating countermeasures, or alerting the vehicle owner and manufacturer. This proactive approach significantly reduces the impact of successful attacks.
Potential Risks Associated with AI in EV Security Systems
While AI offers considerable benefits, its use in EV security also presents inherent risks. A primary concern is the potential for adversarial attacks targeting the AI system itself. Sophisticated attackers could craft malicious inputs designed to mislead or disable the AI, rendering the security system ineffective. For instance, an attacker might introduce carefully crafted noise into sensor data to mask malicious activity, or manipulate training data to compromise the AI’s accuracy.
Another risk is the “black box” nature of some AI algorithms, making it difficult to understand their decision-making processes and identify potential weaknesses. This lack of transparency can hinder efforts to ensure the reliability and security of the AI system. Finally, the reliance on AI for critical security functions creates a single point of failure. If the AI system is compromised, the entire vehicle’s security could be jeopardized.
Comparison of AI-Based and Traditional Security Methods
Traditional security methods, such as firewalls and intrusion detection systems, rely on pre-defined rules and signatures to identify threats. These methods are often reactive, meaning they only respond to known attacks. AI-based solutions, on the other hand, are proactive and adaptive. They can learn and evolve to detect novel attacks that traditional methods might miss. However, AI-based systems require significant amounts of data for training and can be computationally expensive.
The effectiveness of both approaches depends on their proper implementation and maintenance. A hybrid approach, combining the strengths of both traditional and AI-based methods, is often considered the most robust solution.
Hypothetical Scenario: AI Detecting and Responding to an EV Cyberattack
Imagine a scenario where an attacker attempts to remotely access and control an EV’s braking system. A traditional intrusion detection system might detect unusual network activity but may not be able to determine the intent or severity of the attack. However, an AI-based security system, trained on various attack scenarios, would immediately identify the anomalous behavior. The AI would analyze the data, confirm the malicious intent, and automatically initiate countermeasures.
These could include isolating the affected system, alerting the vehicle owner through a mobile app, and notifying the manufacturer’s security team. Simultaneously, the AI might initiate a process to remotely patch the vulnerability and prevent further exploitation, all happening within milliseconds. This swift, automated response would significantly mitigate the risk of a serious accident.
Future Trends and Challenges in EV Cybersecurity
The rapid growth of electric vehicles (EVs) presents a constantly evolving cybersecurity landscape. As EVs become more sophisticated, incorporating advanced driver-assistance systems (ADAS) and increasingly complex software, the attack surface expands exponentially, creating new and unpredictable challenges for manufacturers, consumers, and policymakers alike. Predicting the future of EV cybersecurity requires understanding current trends and extrapolating from them, while also considering the emergence of novel technologies that could either exacerbate or mitigate these risks.
Evolving EV Cybersecurity Threats, EV cybersecurity risks in 2025
The next few years will likely see a significant increase in sophisticated attacks targeting EVs. We can expect more targeted attacks leveraging zero-day vulnerabilities – flaws unknown to developers – to compromise vehicle control systems. Ransomware attacks, already prevalent in other sectors, will likely target EV charging infrastructure and onboard systems, potentially leading to vehicle immobilization or data extortion.
Furthermore, the increasing reliance on connected services and data sharing within the EV ecosystem will create more opportunities for data breaches and privacy violations. For example, imagine a scenario where a hacker gains access to a fleet of autonomous delivery vehicles, disrupting logistics and causing significant financial losses. The scale and impact of such attacks could be far-reaching.
Emerging Technologies for Mitigation
Several emerging technologies hold promise in bolstering EV cybersecurity. Advanced threat detection systems using machine learning (ML) and artificial intelligence (AI) can proactively identify and respond to anomalous activity within the vehicle network. Blockchain technology can enhance the security and transparency of OTA updates, ensuring that only verified and secure software is installed. Formal methods and model checking – rigorous mathematical techniques for verifying software correctness – can significantly reduce the number of software vulnerabilities.
Moreover, the development of secure hardware components, such as hardware security modules (HSMs), can provide an extra layer of protection against attacks targeting software. These technologies represent a significant shift towards a more proactive and resilient approach to EV cybersecurity.
International Cooperation and Standardization
The global nature of the EV industry necessitates international collaboration on cybersecurity standards and best practices. A lack of unified standards could lead to a fragmented and less secure ecosystem, creating opportunities for attackers to exploit inconsistencies across different regions and vehicle manufacturers. International cooperation is vital in establishing shared guidelines for secure software development, data protection, and incident response.
This includes fostering information sharing between governments, industry stakeholders, and researchers to collectively address emerging threats and vulnerabilities. Harmonized standards will be critical to creating a globally secure EV ecosystem.
Recommendations for Policymakers and Industry Stakeholders
To proactively address the challenges of EV cybersecurity, policymakers and industry stakeholders should prioritize the following:
- Mandating robust cybersecurity standards for all aspects of the EV lifecycle, from design and manufacturing to operation and maintenance.
- Investing in research and development of advanced cybersecurity technologies, such as AI-powered threat detection systems and secure hardware.
- Promoting information sharing and collaboration between government agencies, industry players, and researchers.
- Developing comprehensive incident response plans to effectively manage and mitigate cybersecurity incidents.
- Encouraging the adoption of security-by-design principles throughout the EV development process.
- Establishing clear legal frameworks and regulations to address data privacy and security concerns.
- Raising public awareness about EV cybersecurity risks and best practices.
Closing Summary
So, yeah, EV cybersecurity in 2025 is no joke. It’s a complex issue with no easy answers, but by understanding the potential risks and promoting robust security measures, we can help ensure a safer and more secure future for electric vehicles. It’s all about staying ahead of the curve – both for manufacturers and for us, the drivers.
The good news? Awareness is the first step, and continued innovation in security technologies offers a path towards mitigating these threats. Let’s buckle up and get ready for the ride.









